Asp.net Latest Core Patch Release in September 2016
A new patch release for Asp.Net Core 1.0.1 was made by Microsoft in September 2016. This release is claimed to be a long term support release. For programmers, this patch will bring better opportunities because it has updates for many applications of Microsoft including Routing, AntiForgery, and Entity Framework etc.
The security patches are published by Microsoft each month on second Tuesday. These patches helps fixing security issues in various Microsoft products such as Microsoft Windows.
To use the latest version of patch Release, many components of SDK, .Net Framework and Windows Hosting needs to be installed. All release notes the links to common issues are available on GitHub.
Executive Summary
- In September 2016, total 14 security bulletins were released by Microsoft.
- Out of these 14 bulletins, 7 of them were rated with 'important' rating while remaining 7 were rated with critical rating.
- The products affected includes the Microsoft office, Internet Explorer, Microsoft Exchange and Microsoft Windows.
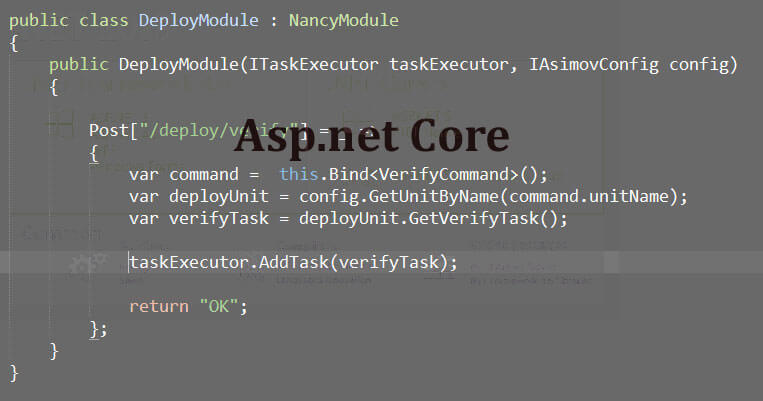
Updates in .Net Core 1.0.1
- Linux 4.6 Segfaults.
- Windows access violation.
- Template for F# is updated.
- Core templates of ASP.NET are updated for adding references to .Net Core 1.0.1.
- Core templates of ASP.NET updated to publish all CSHTML files correctly.
Following are the updates made in Entity Framework and ASP.NET core releases for version 1.0.1. These can be implemented by adding references to updated Nuget packages.
- FIPS Compliance update in MVC.
- Mapping errors of HTTP verbs-GET and DELETE.
- The response body and its specific stream is also replicated in the future requests for few scenarios.
- Several updates for Entity Framework.
Many updates have been made in .Net Core including MSBuild adoption. Also, the future Release will introduce the .Net Standard 2.0.The September patch version includes fixes for Microsoft Office, VBScript Automation, Flash Player in Adobe, Graphics, Edge etc. The most important fix in this patch is the fix of VBScript as suggested Lane Thames, a researcher in Security. Also, there is a patch drop for September Release for MS16-104 and MS16-116.
MS16-116 includes execution vulnerability of remote code in Automation of OLE for the scripting engine of VBScript. Windows, SMBv1 server and Silverlight have fixes for code execution and classed as 'important' similar to the Window kernel and the Window lock screen.
Update of Existing Applications
In order to update the existing application, open the project.json file of your project and update the references of the .Net Core Package to the latest Asp.Net core versions. Also, it is required to update the Entity Framework 1.0.1 and ASP.Net Core 1.0.1 by adding references to the newer Nuget packages.
As intimated by Microsoft, the IISIntegration package has not been updated in the latest release. However, if programmers have added any reference to IISIntegration package, then following versions should be updated:
- Microsoft.AspNetCore.Antiforgery
- Microsoft.EntityFrameworkCore
- Microsoft.AspNetCore.MVC
- Microsoft.aspNetCore.Routing
- Microsoft.AspNetCore.Server.Kestrel
The Antiforgery and the Routing packages can be referenced from the MVC package. Even if they are not directly referenced in the project, no extra effort needs to be done for updating them. They will be updated automatically by the package manager while updating the MVC package.
It is also possible to "lock in" to a particular version of package by adding reference to complete version number of package.
Updating Machine for .Net Core 1.0.1
Once .Net Core 1.0.1 version is installed on the machine, now there will be two versions of .Net Core on machine, one for .Net Core 1.0.0 and other for 1.0.1. That is, installing the latest .Net Core version does not deletes the previous version or update the recent version.
The patch versions of .Net Core have roll-forward policy. In patch versions, only the reliable updates are included rather than adding any new feature. After installing .Net Core 1.0.1, all the existing apps will use the latest version by default. As a result of this policy, all apps will run on more reliable and secure version of Asp.Net core. The roll-forward policy is applied only to the patch versions.
What To you if a trouble arises with .Net Core 1.0.1 version
In case any issue arises on using .Net Core version 1.0.1, report the same on Github issues in core 267.
Following are few work around options in case any trouble arises with .Net Core version 1.0.1
- Make some apps out of roll-forward policy. This option is good only for short term and helps to determine what is the issue with the working of the app and fixing the issue. Apps configured in this way for a long time may lead to an insecure state. In order to configure an app such that it is not roll-forward, go to its applyPatches property in app.runtimeconfig.json file and set it to false.
- Another approach is to simply uninstall the .Net Core version 1.0.1. It can be done either by installer or go to the 1.0.1 Microsft.NetCore.App directory and delete the same manually. As a result, the machine will now use the version of .Net Core 1.0.0
To uninstall the .Net Core version 1.0.1 on Linux, use package manager if it is installed that way. In case it is installed with a .tar.gz or.zip file, then .Net Core version can be uninstalled by using simple operation for adding or removing files.
Most of the identified bugs didn't have simple workaround. All workaround were possible from discussion and solutions given by the Github issue list participants.
Microsoft new announcement blame with no CVE assigned in Asp.Net development service or .net components. There isn’t a patch for this but every step followed by developers before recoding and redevelopment for updated apps.
